Data generation within enterprise environments continues to accelerate at unprecedented rates. Organizations face the critical challenge of managing vast repositories of unstructured data while maintaining high performance and accessibility. Traditional storage architectures often struggle to accommodate this expansion, encountering severe limitations in throughput and capacity as demand increases. When storage arrays reach their maximum threshold, administrators are forced into expensive forklift upgrades or complex storage silos that hinder productivity and complicate management.
The fundamental issue with legacy storage systems lies in their reliance on centralized controllers. Every read and write request must pass through a single point of coordination, creating a severe choke point when user concurrency or file sizes increase. This architecture inherently restricts scalability, limiting the overall potential of an organization's data infrastructure. Addressing this structural limitation requires a paradigm shift in how storage is provisioned, managed, and expanded over time.
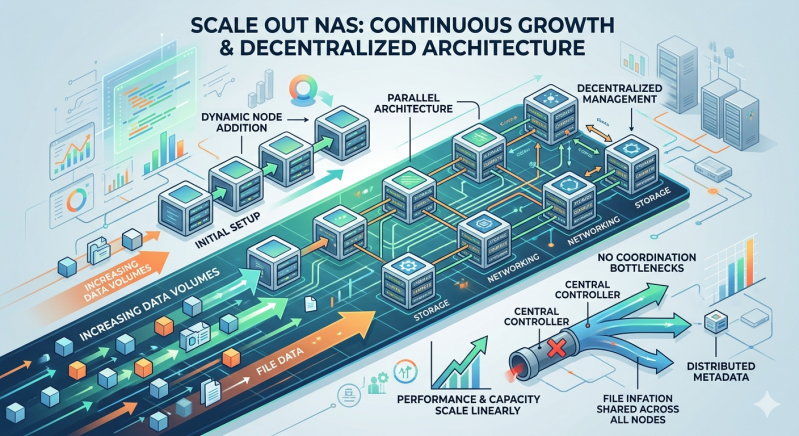
Scale out NAS provides a robust architectural solution to these limitations. By distributing data and processing power across a cluster of interconnected nodes, scale out NAS supports continuous capacity and performance growth without the centralized coordination bottlenecks that cripple legacy systems. This approach allows enterprises to seamlessly expand their storage footprint, adding nodes dynamically while maintaining a unified namespace and consistent performance levels across the entire infrastructure.
Understanding the Evolution of Network Attached Storage
To fully appreciate the advantages of distributed architectures, it is essential to understand the functional mechanisms of traditional Network Attached Storage. Legacy systems operate on a scale-up model. In a scale-up architecture, a primary controller head manages all file system operations, metadata processing, and data routing to attached disk shelves. While adding more disk shelves increases the total storage capacity, the controller head remains static. Eventually, the compute, memory, and network capabilities of that single controller become exhausted.
The Mechanics of Scale Out NAS Architecture
Scale out NAS fundamentally redesigns this operational model. Instead of relying on a solitary controller, a scale out NAS system connects multiple autonomous nodes into a single, cohesive cluster. Each node contributes its own processing power, memory, network bandwidth, and storage capacity to the collective pool. As new nodes join the cluster, the system's aggregate performance and capacity increase linearly.
This clustered approach utilizes a distributed file system to abstract the physical storage hardware from the logical data presentation. Users and applications interact with a single, unified namespace, regardless of where the data physically resides across the network of nodes. When an administrator adds a new node to the scale out NAS cluster, the system automatically redistributes data and client connections to balance the load, requiring zero downtime or manual data migration.
Eliminating Centralized Coordination Bottlenecks
The defining technical advantage of scale out NAS is its ability to bypass centralized coordination. In traditional configurations, every file access request requires the central controller to look up metadata, locate the data blocks, and manage the file lock. This sequential processing model creates latency and queuing delays during peak utilization periods.
Distributed Metadata Management
Scale out NAS resolves this latency by decentralizing metadata management. Metadata—the data about the data, including permissions, file size, and physical location—is distributed across the entire cluster. When a client requests a file, the request is routed to the optimal node based on load balancing algorithms. That specific node can independently process the metadata lookup and retrieve the file blocks without waiting for a central authority to grant permission. This parallel processing capability ensures that performance remains consistent, even as concurrent user connections multiply into the tens of thousands.
Hash-Based Data Distribution
Furthermore, scale out NAS utilizes advanced hashing algorithms to determine data placement. By applying a mathematical function to a file's identifier, the system calculates exactly which node should store or retrieve the data. This eliminates the need for a centralized lookup table that must be constantly updated and queried. Each node independently calculates the data location, enabling massive parallel throughput. This mechanism is critical for supporting bandwidth-intensive workloads, such as video rendering, genomic sequencing, and large-scale data analytics.
Ensuring Robust NAS Security in a Distributed Environment
Transitioning from a centralized storage array to a distributed cluster requires a comprehensive evaluation of data protection protocols. Maintaining stringent NAS Security is paramount when data spans multiple physical nodes. A distributed architecture must enforce access controls and encryption standards uniformly across the entire cluster to prevent unauthorized access and data breaches.
Unified Access Controls and Authentication
Effective NAS Security in a scale out configuration involves integrating the storage cluster with enterprise directory services, such as Active Directory or LDAP. This integration ensures that user authentication and file-level permissions are applied consistently, regardless of which node processes the client request. Scale out NAS systems utilize distributed locking mechanisms and secure client protocols (such as SMB 3.0 and NFSv4) to maintain data integrity and prevent unauthorized modifications during parallel access operations.
Data Encryption and Immutability
Additionally, comprehensive NAS Security requires data encryption both at rest and in transit. Each node within the scale out NAS cluster must support hardware-accelerated encryption to secure data on the physical drives without degrading read/write performance. Furthermore, administrators should implement Write Once, Read Many (WORM) compliance features and immutable snapshots. These security mechanisms protect critical business data from ransomware attacks and accidental deletion, ensuring that historical data states can be rapidly recovered in the event of an incident.
Strategic Implementation for Continuous Enterprise Growth
Deploying a storage infrastructure capable of infinite expansion requires careful planning and a deep understanding of architectural principles. By moving away from scale-up limitations and embracing distributed technologies, organizations can build a resilient foundation for their critical data assets. Network Attached Storage has evolved significantly, and leveraging modern clustered architectures is now a baseline requirement for data-intensive enterprises.
IT leaders must evaluate their current storage utilization trajectories and identify upcoming performance thresholds. Transitioning to a scale out NAS environment allows teams to purchase only the storage they need today, with the assurance that they can add capacity seamlessly tomorrow. Evaluate leading scale out NAS vendors, prioritize comprehensive NAS Security features, and design a deployment strategy that aligns with your organization's long-term data governance policies. Upgrading to a distributed storage model will eliminate existing bottlenecks and empower your infrastructure to support the next decade of digital innovation.
Add comment
Comments